Get Quote
+1-650-281-0558
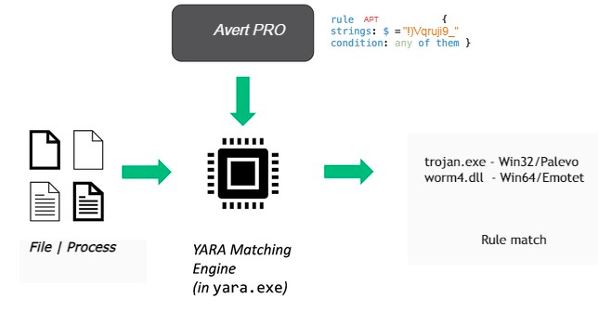
Avert PRO Yara Rules
Developed specifically to hunt APT malware
Customized Detection: Avert PRO rules are tailored for optimal detection of APT threats and the malicious tools used by threat actors, enabling customized detection of specific threats or malware families.
Proactive Threat Identification:By proactively searching for suspicious patterns, APT hunting using Avert PRO enables early detection and mitigation of potential threats before they escalate into security incidents.
Enhanced Visibility:Using Avert PRO for threat hunting provides enhanced visibility into endpoint activity, allowing security teams to identify and investigate anomalies or suspicious behavior that may indicate malicious activity.
Adaptability to Emerging Threats:Avert PRO are updated and refined to adapt to evolving threats and attack techniques, ensuring continuous protection against new and emerging threats.
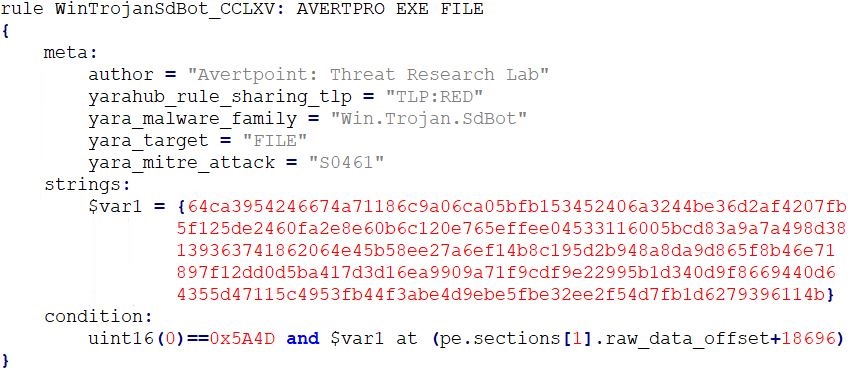
Avert PRO File
Stay One Step Ahead: Threat hunting in endpoints using YARA rules is a proactive approach to cybersecurity that empowers organizations to detect and mitigate threats that evade traditional security controls. By leveraging Avert PRO File YARA rules to proactively search for indicators of compromise and suspicious patterns, organizations can enhance endpoint visibility, identify emerging threats, and strengthen overall security posture. Organizations can maximize the effectiveness of threat hunting in endpoints using Avert PRO File YARA and stay one step ahead of cyber adversaries.
Comprehensive YARA Rules: Avert PRO File YARA rule is based on known threat intelligence, malware samples, and behavioral indicators. Our researchers consider factors such as unique mutexes, pipe names, file hashes, file paths, process names, and network traffic patterns while developing rules.
Continuous Improvement: Rule sets are continuously refined and optimized based on lessons learned, feedback from threat hunting activities, and evolving threat landscape. Our team embraces a culture of continuous improvement to strengthen endpoint security posture over time.
Avert PRO for File Scan: Avert PRO File rules incorporate over 60,000 Yara rules developed by our researchers to hunt APTs and advanced malware, enabling the detection of more than 29,000 malware families.
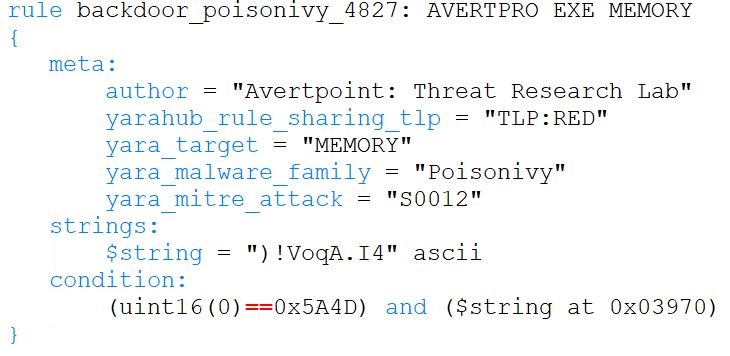
Avert PRO inMemory
Detect the hidden threats: Most parasitic and APT malware reveals its malicious payload only in process memory. When stored on disk as file, this payload is concealed under encryption. Consequently, searching for malicious patterns on the file is ineffective for detecting this type of malware.
Optimized for performance: Yara process scanning is resource-intensive and necessitates highly optimized rules for effective pattern matching. Avert PRO inMemory rules are specifically developed and tested to ensure low resource consumption and rapid scanning.
MITRE ATT&CK: Avert PRO inMemory rules include MITRE ATT&CK information mapped to malware families, adding valuable context to campaigns, tools, and actors associated with it.
Avert PRO for Process memory Scan: Avert PRO inMemory rules detect malware that uses cryptors/packers to evade antivirus software by hunting it in process memory.Our researchers have developed over 60,000 inMemory rules, enabling the detection of more than 18,000 malware families.
Get Updates
Quick Links
Intelligence
Get In Touch
1900 S Norfolk Suite, 350 San Mateo
CA-94403
+1-650-281-0558
All Rights Reserved. © Avertpoint Inc.
