Get Quote
+1-650-281-0558
Avert PRO NDR Rules
Block trojanized c2 in your traffic
In an era of sophisticated cyber threats, organizations must adopt proactive measures to safeguard their networks against malicious activity. Deep Packet Inspection (DPI) has emerged as a powerful tool for threat hunting in network traffic, enabling security professionals to identify and mitigate threats before they escalate into security incidents. This article explores the concept of threat hunting using DPI, its significance in bolstering network security, and best practices for effective implementation.
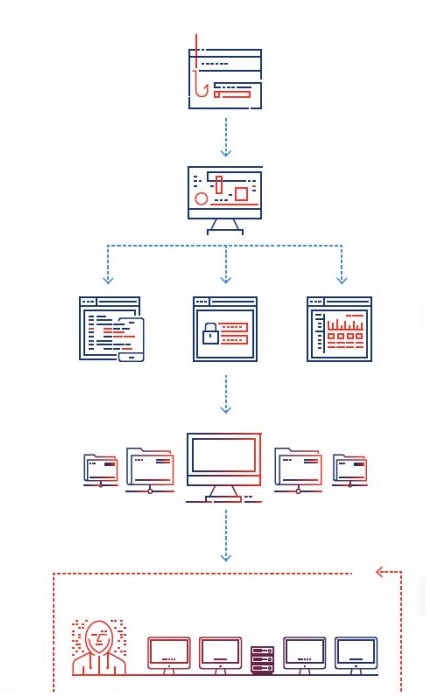
Threat hunting in network traffic involves proactively searching for signs of malicious activity or anomalies within the data packets traversing a network. DPI, a technique that examines the contents of packets at a granular level, enables security analysts to extract valuable insights and identify potential threats. By analyzing packet headers, payloads, and protocols, DPI provides visibility into network behavior, allowing security teams to detect and respond to threats in real-time.

Avert PRO NDR
Enhanced for C2 hunting: Avert PRO NDR rules deep provide visibility into network traffic, identifying malicious activity, unauthorized access, and data exfiltration attempts. By detecting malicious packets in real-time, it enables the detection of C2 as they occur, allowing for immediate response and mitigation.
Identification of Advanced Threats: Avert PRO rules can uncover sophisticated threats that evade traditional security measures, such as encrypted malware, zero-day exploits, and advanced persistent threats (APTs). It also facilitates compliance with regulatory requirements by monitoring network traffic for suspicious activity and ensuring data protection and privacy standards are met.
Proactive Defense: Threat hunting using Avert PRO NDR rules enables organizations to take a proactive stance against cyber threats, reducing the likelihood of successful attacks and minimizing potential damage. It enables continuously monitoring network traffic for anomalies, deviations from normal behavior, and patterns indicative of malicious activity. Use Avert PRO rules to detect unusual traffic patterns, unauthorized access attempts, and suspicious communications that may indicate a security breach.
Continuous Detection Improvement: Our rules set are continuously refined and optimized based on lessons learned, feedback from threat hunting activities, and evolving threat landscape. We embrace a culture of continuous improvement to strengthen network security posture over time.
Avert PRO NDR: Avert PRO NDR rules incorporate ZEEK rules developed by our researchers to hunt APTs and advanced malware, enabling the detection of more than 29,000 malware families, exploits, botnet traffic, exfiltration attempts, trojan access, etc.
Uncover adversaries
Threat hunting in network traffic using Avert PRO NDR is a proactive approach to cybersecurity that empowers organizations to detect and mitigate threats in real-time.
IPS Rules: Our researchers have developed over 75,000 Avert PRO NDR rules which weaponizes your IPS to block anomalies, and uncover potential threats, organizations can enhance network visibility, strengthen defense mechanisms, and reduce the risk of security breaches.
ZEEK Rules: Avert PRO has over 30,000 NDR rules compatible with ZEEK, designed to detect malware, C2 traffic, network worms, trojan payloads, and other malicious activities in your network traffic.

Get Updates
Quick Links
Intelligence
Get In Touch
1900 S Norfolk Suite, 350 San Mateo
CA-94403
+1-650-281-0558
All Rights Reserved. © Avertpoint Inc.
