Get Quote
+1-650-281-0558
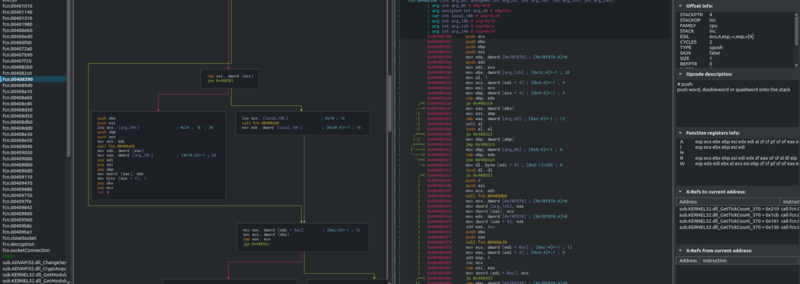
Avert Reverse Engineering
Understand the attacker's intent and potential impact
Malware has many uses for an attacker. Understanding the intent behind it is critical to preventing it from being used successfully against you. Although automated malware analysis tools can provide cursory insight, only human experts can analyze sophisticated malware designed to evade detection. Our expert analysis capabilities are based on global data collection, up-to-the-minute Avertpoint threat detection intelligence. Reverse engineering enables us to analyze behaviors and exploitaion techniques in order to thwart malware’s purposes and help prevent future attacks.
In an ever-evolving landscape of cyber threats, Malware Reverse Engineering stands as a critical pillar in the defence against sophisticated attacks. By dissecting and understanding the anatomy of malware, organizations can better safeguard their digital infrastructure, preemptively detect vulnerabilities, and develop proactive defence mechanisms. In Avertpoint threat research lab skilled professionals employ advanced reversing techniques. By leveraging our expertise, businesses can effectively navigate the complexities of modern cyber threats, strengthening their systems against malicious attacks and ensuring a robust cybersecurity posture.
Why choose Avertpoint
Code Analysis: Experts delve deep into the malware's core, scrutinizing its code structure, functions, and algorithms. This process unveils the inner workings of the malicious software, exposing its intent and potential impact on systems.
Behavioral Understanding: Through reverse engineering, analysts decipher how malware behaves across various environments. This insight aids in predicting and preparing for potential actions, including data theft, system manipulation, or network infiltration.
Vulnerability Identification: Reverse engineering uncovers vulnerabilities and weaknesses within systems exploited by malware. Understanding these entry points is crucial for fortifying security measures and addressing potential breaches.
Countermeasure Development: Insights gleaned from reverse engineering drive the creation of robust countermeasures and defenses. Strategies such as security patches, updated firewalls, and enhanced protocols are formulated to mitigate similar threats in the future.
Enhancement of Threat Intelligence: Knowledge acquired through reverse engineering enriches threat intelligence databases. This information plays a crucial role in identifying, categorizing, and proactively defending against new and emerging threats.
Get Updates
Quick Links
Intelligence
Get In Touch
1900 S Norfolk Suite, 350 San Mateo
CA-94403
+1-650-281-0558
All Rights Reserved. © Avertpoint Inc.